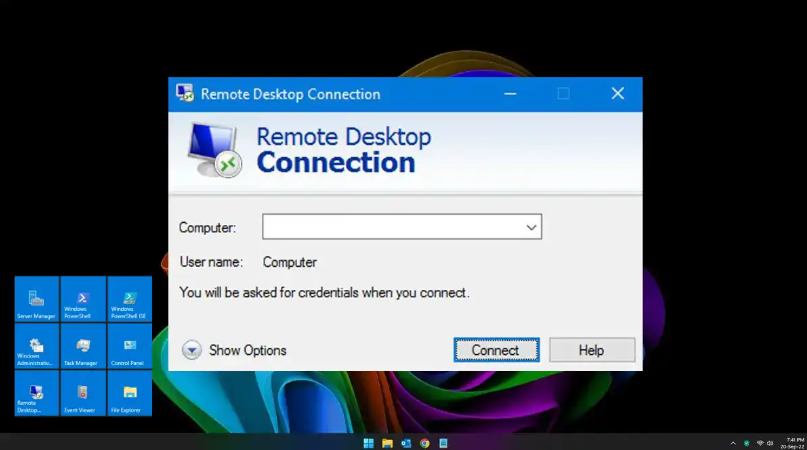
Remote Desktop Protocol (RDP) is a powerful tool that allows users to connect to computers remotely. However, despite its convenience, RDP is frequently exploited by cybercriminals to launch attacks, steal sensitive data, and deploy ransomware. If not properly secured, an open RDP connection can be a gateway for hackers to infiltrate your system. In this post, we’ll explore the key dangers of using RDP and how you can mitigate these risks with essential security measures.
The Dangers of RDP Exploitation
- Brute-Force Attacks: Attackers use automated tools to repeatedly guess passwords, hoping to gain unauthorized access to RDP sessions. Weak or easily guessed passwords make this type of attack highly effective.
- Exploiting Vulnerabilities: Cybercriminals often take advantage of unpatched security flaws in RDP. If your system is not updated regularly, hackers can exploit known vulnerabilities to gain control.
- Ransomware Deployment: Many ransomware attacks begin with compromised RDP access. Once attackers infiltrate a system, they can encrypt files and demand payment to restore access.
- Man-in-the-Middle Attacks: If RDP sessions are not encrypted, attackers can intercept data between the user and the remote machine, potentially stealing credentials or other sensitive information.
How to Secure Your RDP Connection
To protect your systems from RDP-related threats, implement the following best practices:
1. Timely Patching
Always install updates as soon as they’re available. Vendors frequently release patches to address new vulnerabilities, and delaying these updates can leave your system exposed to attacks.
2. Limit Exposure
Restrict RDP access to trusted personnel only. If possible, avoid exposing RDP to the internet entirely and use a VPN or secure gateway instead. Additionally, changing the default RDP port (3389) to a less predictable number can help reduce automated scanning attempts.
3. Use Multi-Factor Authentication (MFA)
Enabling MFA adds an extra layer of security to your RDP sessions. With Network Level Authentication (NLA) and MFA, even if an attacker obtains a valid password, they will still need the additional verification step to gain access.
4. Enforce Strong Passwords
Ensure that all RDP accounts use strong, complex passwords. Passwords should be long, unique, and contain a mix of uppercase and lowercase letters, numbers, and symbols. Implementing a password policy that enforces complexity requirements can significantly reduce the risk of brute-force attacks.
Final Thoughts
While RDP can be a valuable tool for remote access, it also poses significant security risks if not properly managed. By implementing timely patching, limiting exposure, using multi-factor authentication, and enforcing strong passwords, you can significantly reduce the likelihood of cyberattacks. Secure your RDP connections today and keep your systems safe from unauthorized access.